"Ukraine Donors Could Face Federal Prosecution" by George Eliason
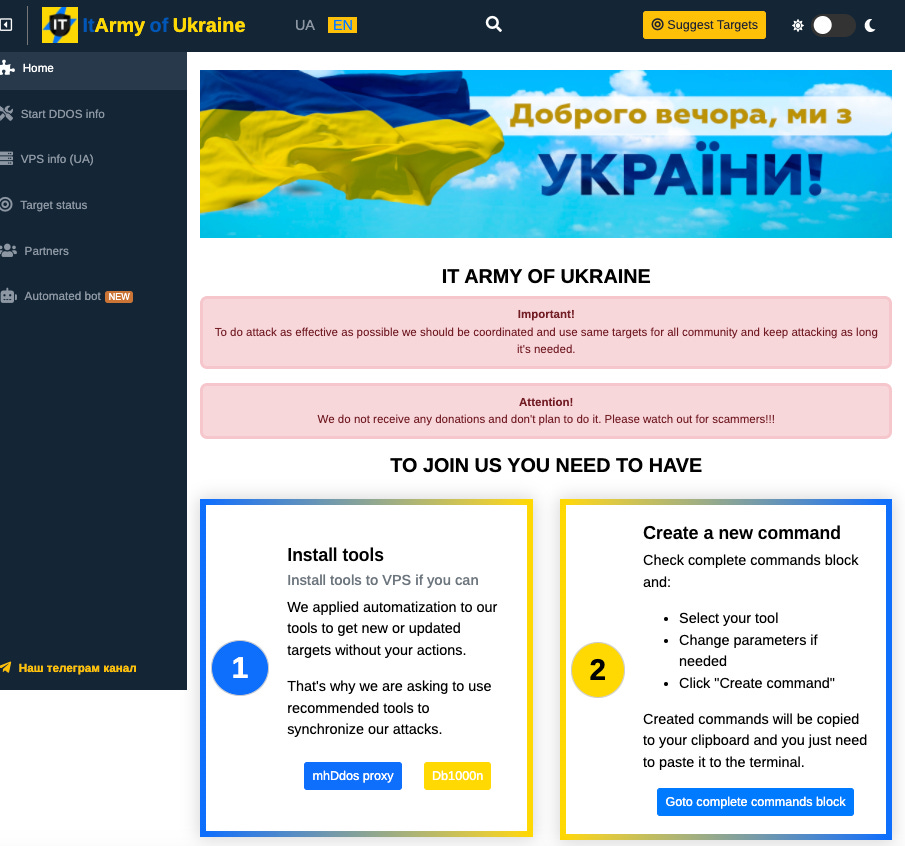
What is the IT Army of Ukraine?
George Eliason’s short video posted 26th August includes important information for internet warriors who are donating to support Ukraine’s military operations. This includes those contributing to the ‘Sign my Rocket' underground crowdfunding industry behind Ukrainian Nazi armed groups which Vanessa Beeley discussed on UK Column News 19th August.
Ukraine neglected to tell donors they are committing state, federal, and international arms dealing crimes for the sign the shell or rocket donor campaign Ukraine is running. Here are the details... – George Eliason
As one person rightly commented on George’s video:
Blimey, When people wanted to buy Canadian Truckers a drink and some fuel to keep warm... all Hell Broke loose! BUT Now people can Adopt a Shell? and that is FINE?
For ease of reference, this is a screenshot of the document which George included at the end of his video.
This is the article linked at the bottom of the screenshot.
The Cyber Combatant: a New Status for a New Warrior
by Maurizio D’Urso published 31 March 2015
Philosophy & Technology volume 28, pages475–478 (2015) Cite this article
Cyber warfare differs from traditional forms of conflicts, both in the instruments used—computers—and in the environment in which it is conducted—the virtual world of the internet and other data communication networks.
The purpose of the commentary is to discuss whether, even in cyber warfare, the concept of ‘direct participation in hostilities’ is still operative, with special reference to the laws related to it, and to assess its consequences with regard to the law of armed conflict. In particular, I will consider whether in cyber warfare the distinction between lawful combatant and unprivileged combatant is still valid. Standing on the premises that this distinction does not apply to non-military combatants in the cyber domain and that any civilian who is taking part in cyber warfare takes direct part in the hostilities as an unlawful cyber combatant, this commentary dwells on the concept of continuous combat function and applies it to cyber combatants. This will offer the ground to address the question as to whether a virtual network, an online forum where members share methods on the way to conduct cyber attacks against a common enemy, could be assimilated to a terrorist organisation whose members have a continuous combat function.
The Cyber Combatant’s Status
The status of lawful combatant is defined in Article 1 of the Regulations concerning the Laws and Customs of War on Land, The Hague, 18 October 1907:
‘Article 1. The laws, rights, and duties of war apply not only to armies, but also to militia and volunteer corps fulfilling the following conditions:
To be commanded by a person responsible for his subordinates;
To have a fixed distinctive emblem recognisable at a distance;
To carry arms openly; and
To conduct their operations in accordance with the laws and customs of war’.
This rule is also reproduced in the Article 4 of the Convention (III) relative to the Treatment of Prisoners of War. G Geneva, 12 August 1949.
According to The Hague ‘jus in bello’ and Geneva Conventions, any combatant who does not match all four of the conditions set in Article 1 is considered an ‘unlawful’ combatant. Meaning that, in case of capture by the enemy, he is not entitled to claim the rights granted to prisoners of war by Convention III relative to the Treatment of Prisoners of War, Geneva, 12 August 1949.
The issue concerning the status is in itself quite complex. It becomes even more so when non-military cyber combatants are under consideration. Especially if cyber combatants operate using computers only, they lack a basic requirement to be considered as lawful combatants: a computer is not considered a weapon, and thus they do not carry arms openly, as is required to be distinguished from civilian population.
A civilian hacker, in order to be distinguished from a member of the civilian population, should also wear a fixed distinctive emblem recognisable at a distance. Nonetheless, in reality it is difficult to imagine civilian cyber combatants wearing a distinctive emblem when they operate from their computers inside civilian buildings. The problem of the distinction between cyber combatants and the general population is evident. The dual-use problem makes the matter even more complex, making indistinguishable computers used for civilian purposes and computers deployed to perpetrate cyber attacks.
On the basis of the above considerations, it can be affirmed that a non-military cyber combatant is an unlawful combatant in almost all cases, with consequent strict limitations on the prerogatives and rights that one may have against the enemy in the event of capture and detention. The current situation is thus paradoxical, as the combatant who uses conventional weapons and lethal force, and may cause severe physical damage and harm, is more protected by International Humanitarian Law than a cyber combatant.
Direct Participation in Cyber Hostilities by Virtual Communities
Assuming that members of non-military cyber organisations cannot be considered lawful combatants, they have to be regarded as unlawful and unprivileged combatants who take part in hostilities. Regarding participation in cyber hostilities, the Tallinn Manual (states in Rule 29 that ‘Civilians are not prohibited from directly participating in cyber operations amounting to hostilities, but forfeit their protection form attacks for such time as they so participate’).Footnote1
This rule derives from Article 51 AP1 93, 3rd paragraph:
‘Civilians shall enjoy the protection afforded by this Section, unless and for such time as they take a direct part in hostilities’.
Therefore, those civilians who participate directly in hostilities lose their general protection against the dangers of military operations and may be attacked for such time as they do so.
According to the Guidance on Direct Participation in Hostilities provided by the International Committee of the Red Cross, the notion of direct participation requires the following three cumulative elements:
‘The act must cause harm to the military operations or military capacity of a party to an armed conflict or, alternatively, inflict death, injury, or destruction on persons or objects protected against direct attack (threshold of harm);
Here must be a direct causal link between the act and the harm (direct causation);
The act must cause harm in support of a party to the conflict and to the detriment of another (belligerent nexus)’.
Time and continuity are another elements, which play a decisive role in considering a civilian taking part to hostilities as lawful target.
Being a member of an organised armed group means that the person assumes a continuous function for the group involving his or her direct participation in hostilities (‘continuous combat function’). The continuous combat function is the mission of irregular combatants groups, whose members aim to fight the enemy indefinitely until his/her defeat. This is the group’s mission and it is permanent and unlimited as long as hostilities last. The continuous combat function requires lasting integration into an organised armed group. Resembling soldiers of regular armed forces, members of an organised armed group who have a continuous combat function may be attacked at any time.
Those conducting hostilities face the difficult task of distinguishing cyber combatants who are engaged in a specific hostile act (direct participation in hostilities) from members of organised armed groups (continuous combat function). This difficulty is evident when considering the issue of direct participation in hostilities of members belonging to virtual communities, like forums or chat rooms, or individuals who are members of groups inside popular social networks—e.g. Facebook, Google or Twitter, exchanging malware and tips on conducting cyber attacks.
Continuous combat function is ascribed to the following:
The administrators of the community, those who have organised the community and who give its members permission to use its services
The advisors and the supporting staff that provide services and technical support
The so-called ‘senior members or moderators’—members distinguished from the others by the quality and quantity of their contribution in the community
All the other members do not have this continuous combat function and could be attacked only if and when they take part in hostilities on the basis of the three parameters of threshold of harm, direct causation and belligerent nexus.
Conclusions
The existing rules of international law are not capable of countering cyber warfare activities. The current regulations posed by the International Humanitarian Law do not allow a civilian cyber combatant to be considered a lawful combat, causing a tremendous disparity of treatment in the case of capture and detention when compared with a ‘regular’ lawful civilian combatant using conventional weapons. This is unfair in equity or in ethics. It raises a plethora of regulative as well as ethical issues that urgently need attention from both the academic and the non-academic world.
Another problematic disparity arises when considering that, according to the International Humanitarian Law, a cyber combatant can be neutralised not only by cyber attack but also by the use of kinetic force, even lethal force if necessary. The principle of proportionality usually refers to the use of the minimum force required to accomplish the mission and neutralise the combatant. In case of a fight between cyber combatants and conventional combatants, the disproportion between the means used by one side against the other is clear and cumbersome.
It would be worthwhile to consider amending the Geneva Conventions and Additional Protocols in order to fit this brand new genre of combatant, whose status remains uncertain.
Notes
Schmitt, Tallinn Manual on the International Law applicable to Cyber Warfare, (CUP 2013), p. 104
Author information
Authors and Affiliations
Italian Defence General Staff, Legal Affairs General Office (SMD–UGAG), Rome, Italy
Maurizio D’Urso
Corresponding author
Correspondence to Maurizio D’Urso.
What is the IT Army of Ukraine?
From that font of information if it suits the agenda, Wikipedia:
The IT Army of Ukraine (Ukrainian: IT-армія України) is a volunteer cyberwarfare organisation created at the end of February 2022 to fight against digital intrusion of Ukrainian information and cyberspace after the beginning of the Russian invasion of Ukraine on February 24, 2022.[1][3] The group also conducts offensive cyberwarfare operations, and Chief of Head of State Special Communications Service of Ukraine Victor Zhora said its enlisted hackers would only attack military targets.[4]
Formation
On 26 February 2022, the Minister of Digital Transformation and First Vice Prime Minister of Ukraine, Mykhailo Fedorov announced the creation of the IT Army, which is mainly coordintating its efforts via Telegram.[5]
According to Reuters, the Ukrainian government asked for volunteers from the country's hacker underground to help protect critical infrastructure and conduct cyber spying missions against Russian troops. Yegor Aushev, the co-founder of a Ukrainian cybersecurity firm Hacken,[6] wrote, "Ukrainian cybercommunity! It's time to get involved in the cyber defense of our country," asking hackers and cybersecurity experts to submit an application listing their specialties, such as malware development and professional references.[7]
Aims
The volunteers who joined the group are divided into offensive and defensive cyber units. While the offensive volunteer unit would help Ukraine's military conduct digital espionage operations against invading Russian forces, the defensive unit would be employed to defend infrastructure such as power plants and water systems.[1]
The Ukrainian government used Twitter and Telegram to share a list of Russian and Belarusian targets for the army to attack.[8] Russian ransomware operators responded by offering their assistance to counter the Ukrainian effort.[9]
Activities
Fedorov requested the assistance of cyber specialists and tweeted a Telegram with a list of 31 websites of Russian business and state organizations.[10][11][5]
On 28 February 2022, the IT Army hacked the website of the Moscow Stock Exchange. The IT Army posted that it had taken them only five minutes to render the website inaccessible.[12][13][14]
On the same day, the IT Army hacked the website of Sberbank, the largest bank in Russia. The IT Army had also launched attacks on other Russian and Belarusian sites, including the government websites of Russia and Belarus, the FSB and the Belarusian state news agency BelTA, among others.[11][15]
According to Reuters, the group targets Russian power grids and railways to prevent Russian infrastructure from reaching Ukraine.[2] This included technologies such as GLONASS.[2]
Eight hundred Russian websites, including Roscosmos, were attacked by the IT Army, from June 27 to July 10. They posted congratulatory messages to Ukrainian Constitution Day on those websites. Besides that, distributed denial of service attacks carried out by the IT army has crippled Russian ability to work on some CRM systems for extended periods.[16]
Ministry of Digital Transformation reported about cyberattacks on over 6000 of Russian web resource in the period from February 26 to July 30.[17]
On the 28th of February MSNBC promoted the IT Ukrainian Army by interviewing Alex Bornyakov, Ukraine's Deputy Minister for Digital Transformation who “joins Joe Scarborough and Mika Brzezinski to discuss how his country is using an "IT Army" to fight Russian disinformation and cyber attacks.”
It is interesting to note that Alex Bornyakov’s LinkedIn profile states that he obtained his MBA from the University of New Brunswick, Canada and a Master of Public Administration – MPA, International Economic Policy and Administration from Columbia in 2019.
Bornyakov lists that he is the co-founder of Adtelligent in the Greater New York City Area (January 2018 to present); a partner in Intersog (Chicago) since 2014; and a Managing Director for Wannabiz – Odessa coworking space, since 2012.
Here is an excerpt from Forbe’s 1st March article, Ukraine’s Propaganda Offensive, Led By Ad-Tech Entrepreneurs, Appears To Be Winning
A few years ago, Alex Bornyakov was a marketing tech entrepreneur. Now, on his 40th birthday, he's helping lead a propaganda war against Russia. UKRAINE’S MINISTRY OF DIGITAL TRANSFORMATION
As Ukraine’s cyber army takes the war to Russian banks and government websites, it’s working with Elon Musk to set up satellite internet. Two former ad-tech entrepreneurs are leading the country’s information warfare charge. Outside experts think they’re winning.
A mere two weeks ago, the former advertising entrepreneurs who run Ukraine’s Ministry of Digital Transformation were focused on making the Kyiv government more accessible by smartphone. Last week, they organized a crowdsourced cyber army, claiming to have knocked Russia’s biggest bank off the internet. This week, it was back to smartphones. They’re distributing an app that’s essentially an air-raid siren to warn Ukrainians of Russian attacks from the sky.
So many lives have utterly changed in the seven days since Russian President Vladimir Putin ordered Russian forces to invade Ukraine. The two former ad-tech executives who helm Ukraine’s digital ministry are no exception. The chief, 31-year-old Mykhailo Fedorov, has gone from being best-known for handling advertising for Ukraine President Volodymyr Zelensky’s 2019 election campaign to, now, being the face of Ukrainian cyber resistance. In the last 24 hours, he’s claimed his cyber army is waging an unprecedented online war and posted online images of himself with freshly-imported satellite-link equipment donated by Elon Musk so the country can maintain an online presence.
(Cont’d…)
On 9th March Yahoo Coin Desk reported, Ukraine Has Received Close to $100M in Crypto Donations
Ukraine has received a total of "close to $100 million" in crypto donations, according to Alex Bornyakov, Ukraine’s deputy minister at the Ministry of Digital Transformation and the de facto crypto spokesperson of the government.
Speaking in an emergency online briefing entitled "Digital Resistance: How Ukraine Is Leveraging Technology to Fight for Freedom," Bornyakov said that more than $60 million of the $100 million was received in the main fund run by Kuna, the Ukrainian crypto exchange.
The rest of the money has been sent to several other smaller funds, Bornyakov indicated.
Asked by CoinDesk if Ukrainian President Volodymyr Zelensky had a view on the role of crypto in the war, Bornyakov said that while Zelensky has not said anything to him about the crypto fund specifically, "he shares our vision" that the use of crypto could be a "breakthrough from an economic standpoint" and that "we have the total support of the president at this point."
Bornyakov said he did not know if anyone in the American government had spoken to anyone in the Ukrainian government about the role of crypto in the war.
In an interview on CoinDesk TV's "First Mover" on Tuesday, Bornyakov repeated his request that crypto businesses cut services to Russian users as part of an unprecedented effort to cut Russia off from the global financial system.
The funds sent to Kuna are reportedly being spent on non-lethal equipment, including fuel, food and bulletproof vests for soldiers, Kuna's founder Michael Chobanian told CoinDesk in an interview last week.
What if any safeguards are in place to ensure that crypto donations are being spent on non-lethal equipment only?
✦✦✦
If you haven’t already, please listen to Vanessa’s discussion of the ‘Sign My Rocket’ underground crowdfunding industry which is supporting Ukrainian Nazi armed groups:







What about governments around the world giving billions in armaments and money to the Ukraine war effort? Of course, all without consulting their citizens.
All is fair in love and war.